HOW DOES A WAF WORK?
A Web Application Firewall (WAF) filters, monitors, and blocks HTTP traffic to and from a web application. While regular firewalls serve as a safety filter between servers, a WAF can filter the content of specific web applications. By inspecting HTTP traffic, it can prevent attacks stemming from web application security flaws, such as SQL injection, Cross-Site Scripting (XSS), Cross-Site Request Forgery (CSRF) and security misconfigurations. When used in environments such as e-commerce platforms and enterprise portals, a WAF is one of the most important security elements to defend the entire platform against attacks.
This article not only describes a solution which can easily be used on the Open Telekom Cloud but also shows how to deploy this approach. The Open Telekom Cloud already provides an anti-DDoS service which compliments and enhances the customer’s whole security solution. Our solution is composed of Open Telekom Cloud public cloud capabilities and the Imperva WAF product. Please note that the Imperva license and application has to be purchased then downloaded separately.
RECOMMENDED ARCHITECTURE FOR LEVERAGING WAF IN THE CLOUD
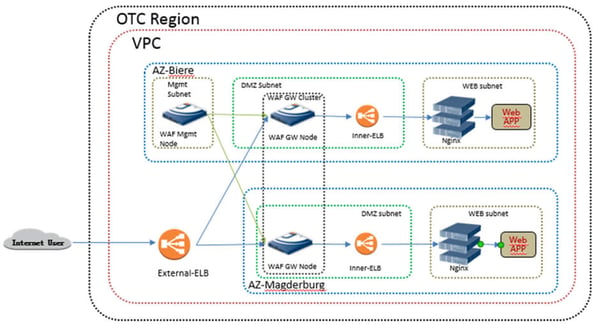
End users send access requests to an external ELB (Elastic Load Balancer). This ELB forwards the traffic to several WAF gateway nodes. All WAF gateway nodes and the management node are in one VPC, but in different subnets. As the solution is based on cross AZ (availability zone) architecture, each AZ has one gateway node. The WAF gateway connects to Web APP through reverse proxy mode. The Nginx servers shown are an optional element of the solution. In the next section, we will examine the resources needed to deploy the suggested architecture on Open Telekom Cloud.
RESOURCES REQUIRED TO DEPLOY THE ARCHITECTURE
The set-up requires three elastic compute servers (4 vCPU/16 GB RAM), one VPC with three subnets and an NSG (Network Security Group in VPC), and additionally an external ELB. Furthermore, Imperva software is essential; one Imperva SecureSphere WAF V 2500 Management for Xen in the management subnet, and two Imperva SecureSphere WAF AV 2500 Gateway for Xen in the DMZ subnets (for the gateways).
DEPLOYMENT
How use a Web Application Firewall (WAF) solution – TelekomCLOUD
Deployment is undertaken in four steps, beginning with resource preparation. Initially, you should create your VPC and subnets, followed by creating and configuring the NSG. Add the external ELB and optionally deploy an inner VM for domain name service, if you need a domain name resolution.
The second step focuses on image import; create a temporary VM and import the WAF app package to the data disk on this VM. Decompress the package, shut down the temporary VM and re-mount the data disk as a system disk. Start the temporary VM and create a private image.
The third step initializes the device; begin with a WAF gateway node then initialize the WAF management node.
To check the deployment, run a web console test. Log in to the WAF management console and check the gateway status. As the console is web-based, you can log in with the default URL provided by WAF.
AT A GLANCE: THE BENEFITS OF OPEN TELEKOM CLOUD
- Security: The data are hosted in highly secure Telekom computing centres in Germany.
- Scalability: Computing power and memory can be ordered and set up online and adapted flexibly at any time.
- Pricing Models: We offer you flexible and fixed contractual periods as well as a combination of both models.
- No Vendor Lock-In: Open Telekom Cloud is based on OpenStack, a freely available open-source standard. You can change the provider at any time.
- Individual Configuration: CPU, RAM, storage, network – you can put a package together for yourself that matches your requirements to the optimum degree.
- IaaS for All: Open Telekom Cloud is extremely flexible and therefore suitable for companies of every size.